Malicious Call History Apps Hijacking Mobile Payments Discovered on Official App Stores

Malicious Call History Apps Hijacking Mobile
Cybersecurity researchers have uncovered a sophisticated campaign where deceptive call history management applications were used as a front to intercept sensitive financial data and authorize fraudulent mobile payment transactions.
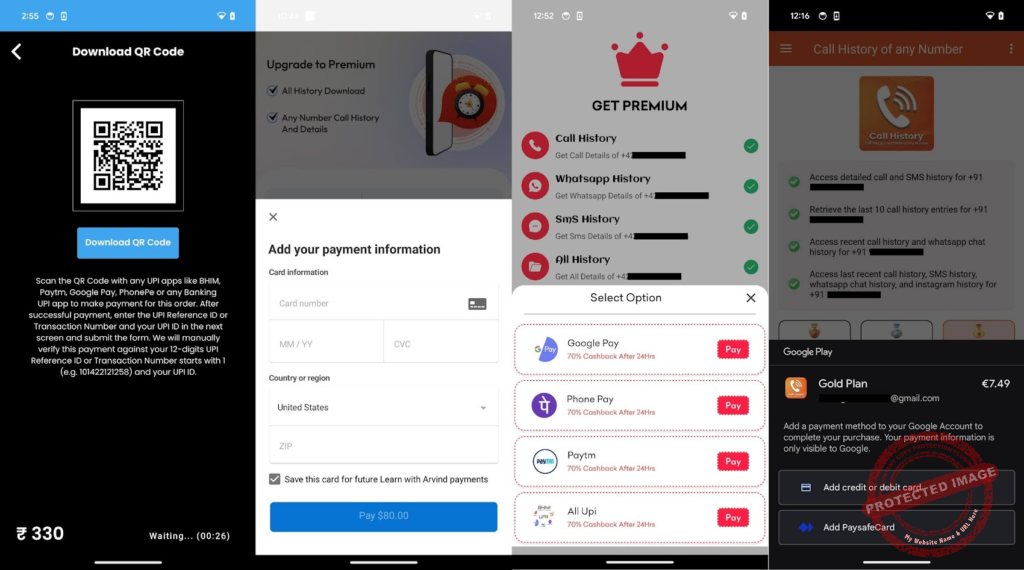
May 9, 2026 | Global: A new wave of mobile financial fraud has been identified involving seemingly harmless utility applications. According to the latest security reports, several “Call History Manager” and “Recent Call Tracker” apps available on major platforms were embedded with high-level spyware designed specifically to target mobile wallets and banking interfaces.
The operation functioned by requesting extensive permissions that appeared logical for a call management app, such as access to SMS and call logs. However, once granted, the malware silently monitored the device for one-time passwords (OTPs) and payment confirmation alerts. By intercepting these short-lived security codes, the attackers were able to bypass two-factor authentication (2FA) and finalize unauthorized transfers directly from the victims’ linked bank accounts.
What makes this campaign particularly dangerous is the use of “overlay attacks.” When a user opened a legitimate banking or payment app, the malicious utility would display a pixel-perfect fake login screen over the real one. Unsuspecting users would enter their credentials into this hidden layer, effectively handing over their account access to remote command-and-control servers. Forensic analysis suggests that the stolen funds were quickly laundered through various cryptocurrency mixers to prevent tracking by financial authorities.

Security experts are urging mobile users to immediately audit their installed applications and revoke permissions for any third-party tools that are not from verified, high-reputation developers. Most of the identified malicious apps have since been removed from official stores, but thousands of devices remain infected. This incident serves as a stark reminder that even basic utility apps can be weaponized into powerful tools for financial cybercrime if users do not maintain strict digital hygiene and limit app permissions to the absolute minimum required for functionality.
Follow us On Our Social media Handles :
Instagram
Youtube
Facebook
Twitter
Also Read- Pune





